Key Takeaways
- Contextual Policies allow AI safety rules to change based on the specific user, environment, and intent.
- Dynamic Guardrails provide real-time monitoring and intervention to stop emerging threats before they execute.
- A defense-in-depth strategy is essential, combining pre-deployment filtering with post-deployment tracking.
- The 2026 risk landscape is dominated by highly realistic deepfakes and AI-assisted cyberattacks that target critical infrastructure.
The New Risk Landscape in 2026
We aren't just dealing with "hallucinations" anymore. According to the International AI Safety Report 2026, which synthesized evidence from over 100 global experts, risks have evolved into three distinct buckets: malicious use, malfunctions, and systemic harms. The most pressing issue is malicious use. We're seeing AI-generated content used for sophisticated blackmail and non-consensual imagery, often targeting women and girls with frightening precision.
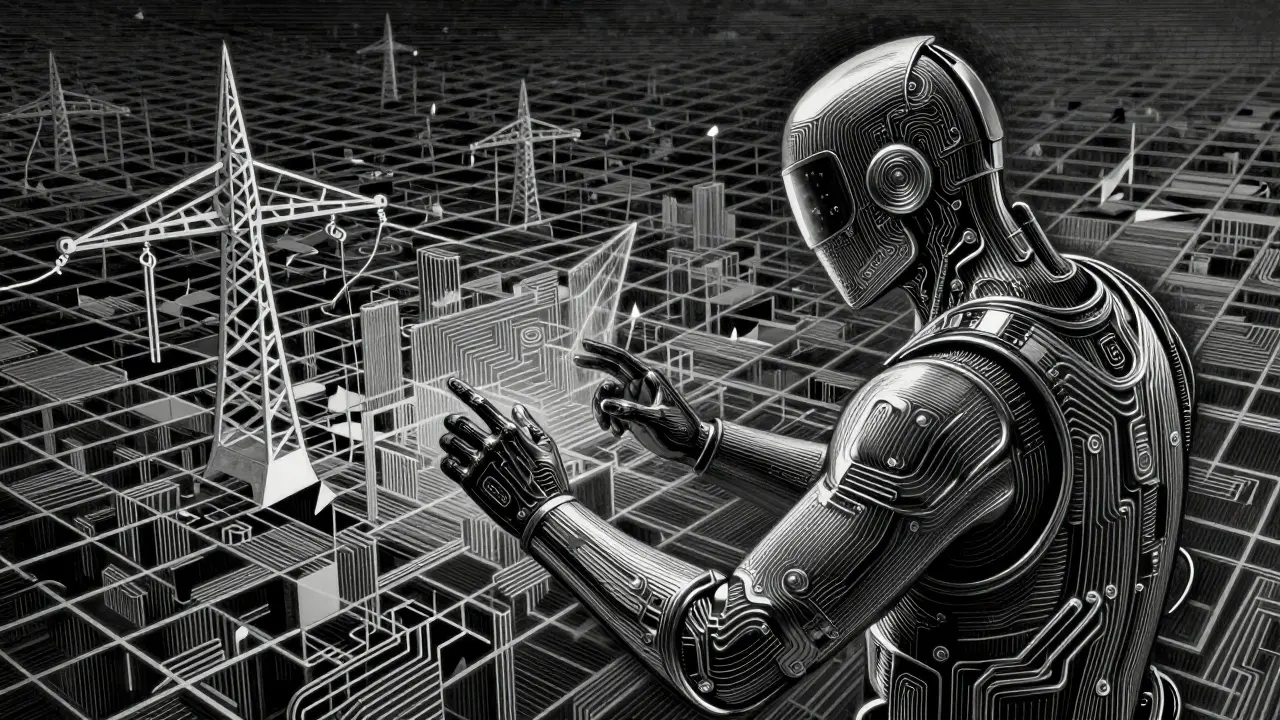
In the world of cybersecurity, the attack surface has exploded. Generative AI can now craft phishing emails that are nearly impossible to distinguish from a real message from your boss. They aren't just generic templates; they use contextually accurate details to fool even the most cautious employees. More worrying is how General-Purpose AI (GPAI) is being used to find software vulnerabilities. While AI isn't usually executing the entire attack autonomously yet, it's doing the heavy lifting in the preparatory stages, making it much faster for hackers to find a way in.
Understanding Contextual Policies
Contextual Policies are adaptive safeguards that adjust their strictness and rules based on the specific deployment context. Think of it like a building's security: the rules for someone entering the lobby are different from the rules for someone entering the server room. Old-school AI safety used a "one size fits all" approach, but that either killed the AI's utility or left it too open.
With contextual policies, the system evaluates the scenario. If an AI is acting as a coding assistant for a verified developer in a secure environment, it might be allowed to generate complex scripts. However, if the same model is accessed by an anonymous user via a public API, the policy tightens. This prevents the model from becoming a tool for creating malware while still remaining useful for professional work. In 2025, twelve major companies updated their Frontier AI Safety Frameworks to move toward this nuanced governance, acknowledging that safety cannot be a static switch.
Dynamic Guardrails: Real-Time Defense
If contextual policies are the "rules of the house," Dynamic Guardrails are the security guards patrolling the halls in real-time. These are technical layers that monitor inputs and outputs continuously, looking for patterns that suggest a prompt injection or a jailbreak attempt. Unlike static filters, dynamic guardrails can evolve as they encounter new attack vectors.
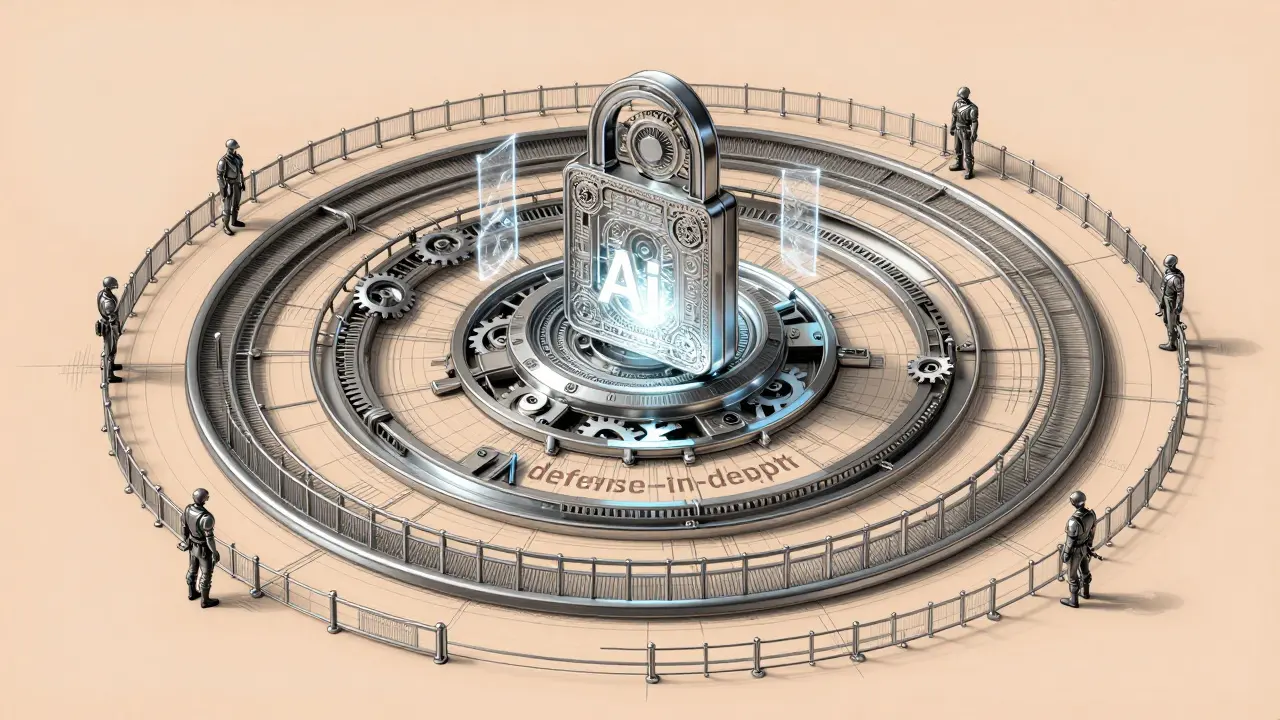
The goal here is defense-in-depth. This means you don't rely on one single wall. Instead, you layer your protections: first, a content filter; then, a capability evaluation; then, a real-time monitor; and finally, an incident response plan. If a hacker finds a way to bypass the first filter, the dynamic guardrail catches the anomalous output before it ever reaches the user. This is critical for open-weight models, where safeguards can often be stripped away by a determined user with enough computing power.
| Feature | Static Safeguards | Dynamic Guardrails |
|---|---|---|
| Response Time | Fixed/Pre-set | Real-time adaptation |
| Flexibility | Rigid (Keyword based) | Context-aware |
| Attack Resistance | Easily bypassed via prompt engineering | Detects evolving behavioral patterns |
| Implementation | Simple filtering | Complex monitoring agents |
The Rise of Security Agents
One of the most interesting shifts in 2026 is the move toward "ambient security." The idea is that every AI agent should have the same level of security protection as a human employee. This means giving each agent a unique identity and strictly limiting its access to specific data sets. If an agent doesn't need to see your payroll data to summarize a meeting, it shouldn't have the technical ability to access it.
We are now seeing the deployment of dedicated security agents-AI designed specifically to hunt other AI threats. These agents perform continuous security testing, looking for data leakage or prompt injections. They essentially act as an automated red-team, trying to break the system so the developers can fix the hole before a real attacker finds it. This transforms security from a "check-the-box" activity into a living, breathing part of the software architecture.
Balancing Innovation and Resilience
For business leaders, there is a constant tug-of-war between speed-to-market and safety. It's tempting to push a new feature live to beat a competitor, but ignoring the safety layer can lead to catastrophic brand damage or legal liability. The most successful organizations in 2026 are those adopting a "secure-by-design" mindset. They aren't adding security at the end; they are building it into the very foundation of the AI pipeline.
A practical rule of thumb for CISOs is to separate input risks from output risks. Input risks involve things like data scraping and malicious prompts, while output risks involve the AI generating harmful content or leaking intellectual property. By auditing these two streams separately, companies can apply the right level of contextual policy to each, ensuring that the AI stays productive without becoming a liability.
What is the difference between a contextual policy and a guardrail?
A contextual policy is the high-level rule set that determines what is allowed based on the situation (e.g., "Medical AI can only give prescriptions to licensed doctors"). A guardrail is the technical mechanism that enforces that rule in real-time, monitoring the actual conversation to ensure the AI doesn't drift into forbidden territory.
Are open-source AI models less safe than closed ones?
Not necessarily, but they present different challenges. Because the weights are open, a user can manually remove the safety filters. This is why dynamic guardrails-which live outside the model itself-are so important for open-source deployments.
What is "defense-in-depth" in the context of AI?
It's a layered security strategy. Instead of one big wall, you use a series of protections: content filtering, identity management for agents, real-time output monitoring, and human-in-the-loop oversight. If one layer fails, the others are there to catch the threat.
How is Generative AI being used to attack critical infrastructure?
Attackers use AI to identify software vulnerabilities in the systems that manage electricity, water, or healthcare. While the AI might not launch the attack, it helps the hacker write the exploit code and craft convincing phishing messages to get inside the network.
Can AI actually help make other AI safer?
Yes. Security agents use generative AI to automate the detection of threats and simulate attacks (red-teaming). This allows defenders to find and patch vulnerabilities much faster than a human team could manually.
Next Steps for Implementation
If you're moving from a pilot project to a full-scale AI deployment, start by mapping your entities. Who is the user? What data is the AI touching? What is the worst-case scenario for a malfunction? Use this map to build your first set of contextual policies.
For those managing existing systems, conduct a "gap analysis" against the International AI Safety Report 2026. Check if you are relying on a single filter or if you have a true defense-in-depth architecture. If you're using open-weight models, prioritize the implementation of external monitoring agents to replace the filters that might have been stripped from the model weights.